MD5 Hash Generator Tool
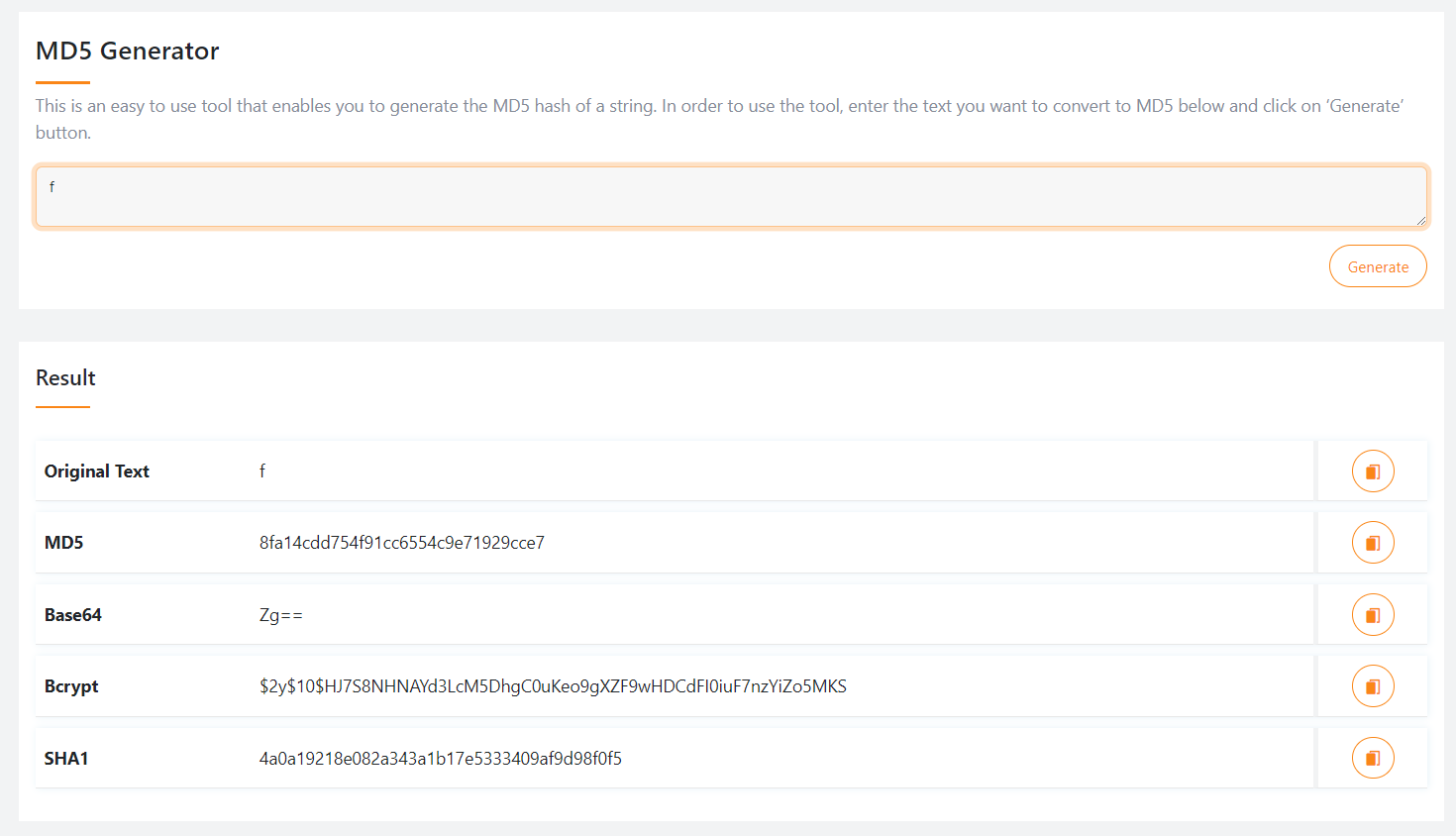
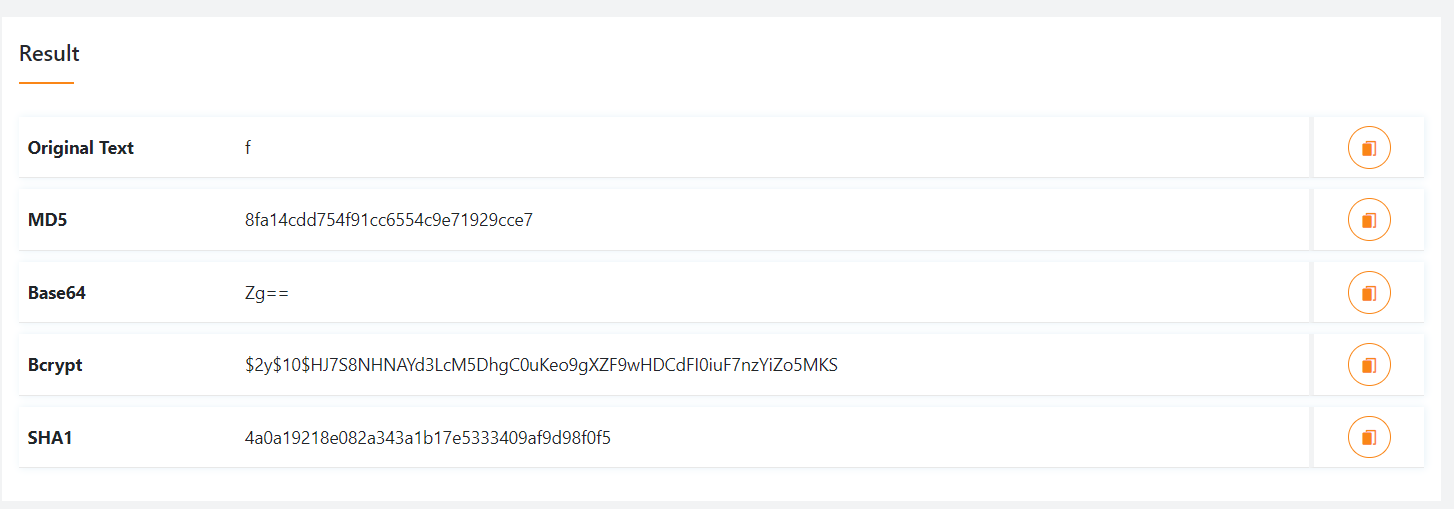
Our MD5 hash generator is a simple and efficient tool designed to convert any text into an MD5 hash instantly. Just enter the string you'd like to hash in the field below and click "Generate" to see the result. This tool is perfect for developers, security enthusiasts, or anyone needing to convert text to an MD5 hash quickly and easily.
Share on Social Media:
An MD5 Hash Generator Tool creates a unique hash value from input data. It ensures data integrity and security.
An MD5 Hash Generator Tool is essential for generating a unique 32-character hash value from any given input. This cryptographic function is widely used for data integrity checks and secure storage of sensitive information like passwords. The tool takes any string of text and converts it into a fixed-length hash, making it nearly impossible to reverse-engineer the original input.
This feature is crucial for verifying the authenticity of files and data in various applications, from software development to cybersecurity. Easy to use and highly reliable, MD5 Hash Generators provide an added layer of security, ensuring that data remains unchanged and protected.
How Md5 Works
Understanding how MD5 works can help you use it effectively. This section explains the MD5 hashing process and its primary use cases.
Hashing Process
The MD5 hashing process converts data into a 128-bit hash value. This means any input, regardless of size, results in a fixed-length hash.
Here's a simple breakdown of the process:
Input data is taken.
The data is divided into 512-bit chunks.
Each chunk undergoes a series of operations.
These operations include bitwise shifts and additions.
Finally, the output is a 32-character hexadecimal number.
Use Cases
MD5 is widely used for data integrity and verification. Here are some common use cases:
| Use Case | Description |
|---|---|
| File Verification | Check file integrity after download. |
| Password Storage | Store passwords in a hashed form. |
| Data Integrity | Ensure data has not been altered. |
While MD5 is useful, it has vulnerabilities. It's important to be aware of these. For highly secure applications, consider stronger algorithms like SHA-256.
Advantages Of Using Md5
The MD5 hash generator tool is widely used in various applications. It offers several advantages that make it a popular choice for data integrity and security. Below, we explore the key benefits of using MD5.
Speed And Efficiency
MD5 is known for its speed and efficiency. It quickly generates a 128-bit hash value. This is especially useful when dealing with large data sets.
MD5 can process large amounts of data in a short time. This makes it ideal for applications where speed is crucial.
| Feature | Benefit |
|---|---|
| Fast Processing | Handles large data sets quickly |
| Efficiency | Generates hash values with minimal resources |
Simplicity
MD5 is simple to implement and use. It requires minimal configuration, making it accessible for developers of all skill levels.
The algorithm is straightforward, requiring only basic coding knowledge. This simplicity ensures that it can be used in a variety of applications without extensive setup.
Easy to implement
Requires minimal configuration
Accessible for all skill levels
Common Applications
An MD5 Hash Generator Tool is widely used in various fields. It ensures data integrity, password storage, and more. Below are some common applications of MD5 hash generators.
Data Integrity
Maintaining data integrity is crucial in digital communication. An MD5 hash generator helps verify the accuracy of transmitted data. It creates a unique hash for the original data. After transmission, the data is hashed again. Both hashes are compared to check for changes.
For example, if you download a file, you can use an MD5 hash to ensure it wasn't altered. The original file's hash is provided. You generate a hash of the downloaded file and compare them. If they match, the file is unaltered.
Password Storage
Storing passwords securely is essential for any application. An MD5 hash generator converts passwords into a unique hash. This hash is stored instead of the actual password.
When a user logs in, their password is hashed again. The new hash is compared to the stored hash. If they match, the user gains access. This process ensures passwords are never stored in plain text.
Here is a simple table showing the process:
| Step | Action | Result |
|---|---|---|
| 1 | User creates a password | Password: 12345 |
| 2 | MD5 hash generated | Hash: e10adc3949ba59abbe56e057f20f883e |
| 3 | Hash stored | Database stores hash |
| 4 | User logs in | Password: 12345 |
| 5 | New hash generated | Hash: e10adc3949ba59abbe56e057f20f883e |
| 6 | Hashes compared | Access granted if they match |

Md5 Vs Other Hash Functions
Choosing the right hash function is crucial for data integrity. MD5 is a popular choice, but there are other hash functions to consider. This section compares MD5 with other hash functions.
Sha-1
SHA-1 stands for Secure Hash Algorithm 1. It's more secure than MD5. SHA-1 produces a 160-bit hash value. This is longer than MD5's 128-bit hash. SHA-1 is commonly used in SSL certificates.
MD5 is faster but less secure than SHA-1. SHA-1 is less prone to collisions. Collisions happen when two inputs produce the same hash. Here’s a quick comparison:
| Hash Function | Hash Length | Security | Speed |
|---|---|---|---|
| MD5 | 128-bit | Less Secure | Faster |
| SHA-1 | 160-bit | More Secure | Slower |
Sha-256
SHA-256 is part of the SHA-2 family. It produces a 256-bit hash value. This is double the size of SHA-1. SHA-256 is much more secure than MD5. It's widely used in blockchain technology.
MD5 is quicker but less secure. SHA-256 offers strong security. It is harder to break. Here’s another quick comparison:
| Hash Function | Hash Length | Security | Speed |
|---|---|---|---|
| MD5 | 128-bit | Less Secure | Faster |
| SHA-256 | 256-bit | Highly Secure | Slower |
Choosing the right hash function depends on your needs. For speed, MD5 is the best. For security, choose SHA-1 or SHA-256. Both offer better security than MD5.
Limitations Of Md5
MD5 is a popular hashing algorithm. It has many applications in data integrity and authentication. But, it has several limitations that you should know.
Security Concerns
The primary issue with MD5 is its lack of security. The algorithm is vulnerable to several types of attacks. Hackers can exploit these vulnerabilities to compromise data.
MD5 does not provide adequate protection for sensitive information. Experts recommend using stronger hashing algorithms like SHA-256 or SHA-3.
Collision Vulnerabilities
Another major problem is collision vulnerabilities. A collision occurs when two different inputs produce the same hash value. This flaw undermines the reliability of MD5.
Collision attacks make it easier for attackers to create fake data that matches the hash of legitimate data. This can lead to data breaches and loss of trust.
| MD5 Issue | Description |
|---|---|
| Security Concerns | Vulnerable to several types of attacks. |
| Collision Vulnerabilities | Two different inputs can produce the same hash. |
To safeguard your data, consider using more secure algorithms. Avoid relying on MD5 for cryptographic purposes.
Choosing An Md5 Hash Generator Tool
Choosing the right MD5 Hash Generator Tool is crucial for your needs. The right tool ensures data integrity and security. Below, we discuss important features and popular tools.
Key Features To Look For
Not all MD5 Hash Generator Tools are created equal. Here are some key features to consider:
Ease of Use: The tool should have a user-friendly interface.
Speed: Fast processing is essential for large files.
Accuracy: The tool must generate accurate MD5 hashes.
Compatibility: Ensure the tool supports various file formats.
Security: The tool should provide secure hash generation.
Popular Tools
Here are some popular MD5 Hash Generator Tools that meet these criteria:
| Tool Name | Key Features |
|---|---|
| MD5 Online | Easy to use, fast, and supports multiple file formats. |
| HashCalc | Accurate, compatible with various files, and secure. |
| QuickHash | User-friendly, speedy processing, and high accuracy. |
Choose the tool that best fits your needs. Consider the key features and your specific requirements. Always prioritize accuracy and security in your selection.
Step-by-step Guide To Using An Md5 Generator
Understanding how to use an MD5 Hash Generator Tool can simplify your data encryption needs. This guide will walk you through the process.
Inputting Data
First, locate a reliable MD5 generator tool online. Open the tool in your browser. You'll see a text box or field.
Now, input the data you want to hash. This could be a password, file name, or any text.
Simply type or paste your data into the input field. Ensure the data is correct before proceeding.
Generating The Hash
Next, click the "Generate" button or similar option. The tool will process your data.
Within seconds, you will see an MD5 hash displayed. This is a string of characters representing your data.
Copy this hash to use as needed. Always verify the hash for accuracy.
Here's a sample table showing input and output:
| Input Data | MD5 Hash |
|---|---|
| example | 5d41402abc4b2a76b9719d911017c592 |
| password | 5f4dcc3b5aa765d61d8327deb882cf99 |
Using an MD5 generator is straightforward. Follow these steps to secure your data.
Frequently Asked Questions
What Is An Md5 Hash Generator?
An MD5 hash generator creates a unique string of characters (hash) for a given input. It ensures data integrity by detecting changes in the input data.
How Does An Md5 Hash Work?
An MD5 hash converts input data into a 32-character hexadecimal number. Even small changes in input result in a different hash, ensuring data integrity.
Is Md5 Hash Secure For Passwords?
MD5 is not recommended for password storage due to vulnerabilities. Modern algorithms like SHA-256 offer better security and are preferred.
Can An Md5 Hash Be Reversed?
No, MD5 hashes are one-way functions. They cannot be reversed to retrieve the original input, ensuring data remains secure.
Conclusion
An MD5 Hash Generator Tool is essential for securing data. It ensures data integrity by creating unique hash values. Simple to use, it enhances cybersecurity measures. Use this tool to protect sensitive information effectively. Start using an MD5 Hash Generator today to strengthen your data security strategy.